A&S Graduate Studies
[PAST EVENT] Shengye Wan, Computer Science - Ph.D. Oral Examination
Abstract:
In the past decade, Trusted Execution Environment (TEE) provided by ARM TrustZone had become one of the most popular techniques to build security on mobile devices. On a TrustZone-enabled system, the software can execute in either Secure World (trusted) and Normal World (untrusted). Meanwhile, along with the expeditious development of the TrustZone technology, the security of TrustZone-based TEE is also challenged by dealing with more and more on-board hardware and in-TEE applications. In this dissertation, we explicitly study the security of ARM TrustZone technology with the latest ARM architecture in three aspects.
First, we study the security of the TrustZone-based asynchronous introspection. Previously, asynchronous introspection mechanisms have been developed in the secure world to detect security policy violations in the normal world. However, we identify a new normal-world evasion attack that can defeat the asynchronous introspection by removing the attacking traces in parallel from one core when the secure-world checking is performing on another core. As the countermeasure, we propose a trustworthy asynchronous introspection mechanism called SATIN, which can effectively prevent evasion attacks with a minor system overhead by increasing the attackers' evasion time cost and decreasing the defender's inspecting time.
Second, we design an ARM TrustZone-aided connectivity mechanism, called TZNIC, to enable the secure world's access to network even at the presence of a malicious OS. TZNIC deploys two NIC drivers, one secure-world driver, and one normal-world driver, that multiplex one physical NIC. We utilize the ARM TrustZone-based high-privilege to protect the secure-world driver, and further resolve several challenges about sharing one set of hardware peripheral between two isolated software environments. The evaluation shows that TZNIC can provide a reliable network channel for the secure world.
Third, we investigate the memory-safety of secure-world applications. As the existing TrustZone hardware focuses on protecting the application's confidentiality and integrity from malicious software in the normal world, there is little the secure world can do when the inside applications contain vulnerabilities and further get exploited by remote parties. This limitation is particularly important, as the majority of the existing applications inside the TEE are developed in languages without guarantee on memory-safety, such as C, for performance. To enhance the memory-safety of the secure-world application, we plan to propose RusTEE, a TrustZone-based SDK that enables the development of TEE-protected trusted applications with Rust, a memory-safe programming language.
Bio:
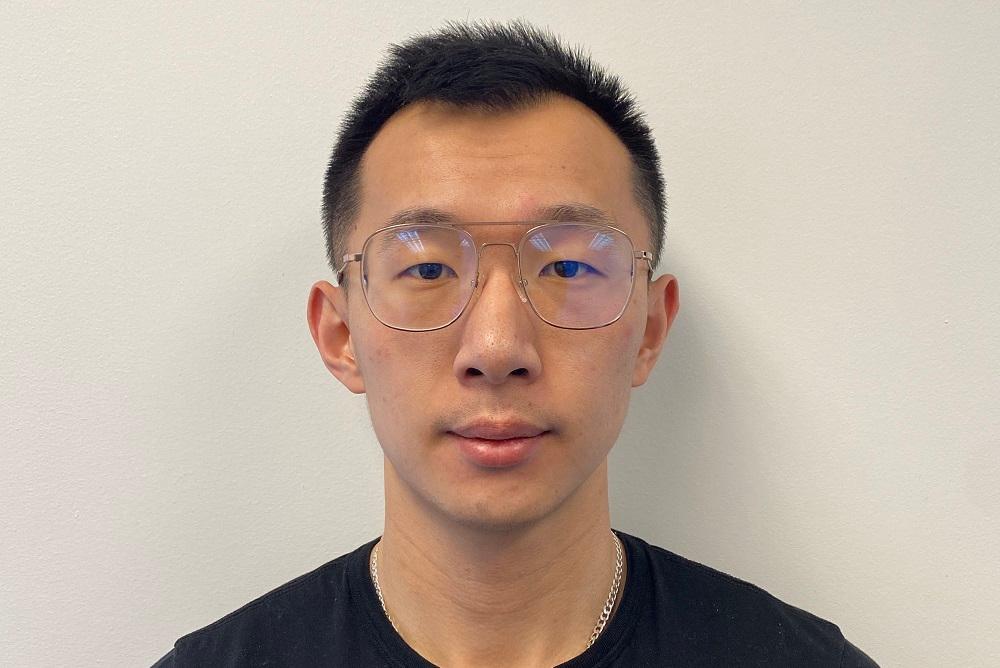
Shengye Wan is a Ph.D. candidate in the Computer Science Department at William & Mary, under the supervision of Dr. Kun Sun. Before that, he received his Master's degree in the Computer Science Department at William & Mary in 2016 and Bachelor of Engineering degree from Software Engineering Department of Huazhong University of Science and Technology in 2014. His research interests lie in computer and network security with a focus on the trusted execution environment on multi-core mobile devices.
